A sordid tale of customer identifiers - the complexity of knowing when we know
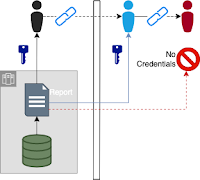
Customer identifiers are the keys we use to bind different bits of information together that we believe represent the same person. This can be more complex than it sounds when you take into account the changing amount of what we know, corporate acquisitions, and partner company interactions. Video Presentation Content Speaker's notes to be added at some future date. A corporation, with divisions that each have apps and with partners. The corporation runs with a single id per person and handles any merge or separation actions by updating all parties. Conway's law: Architecture and communication paths align with organizational structure. Every team does their own thing. Division IDs are bound to the corporate ID at the corporate level. Corporate IDs are bound to the division at the division level. The corporation creates link ids there shared with the other orgs. The other orgs create link ids and share with the parent corporation.