A Chrome Plugin: Highlighting your AWS Account
 I'm working on a set of projects based in AWS. Our projects have somewhere between 7 and 9 different environments representing different levels of software maturity. Production is the most restricted. Development is the least restricted. The rest fall somewhere in between.
I'm working on a set of projects based in AWS. Our projects have somewhere between 7 and 9 different environments representing different levels of software maturity. Production is the most restricted. Development is the least restricted. The rest fall somewhere in between.The company partitions the different levels of their SDLC into separate AWS accounts. Each account can have multiple environments that are of similar concerns and access controls.
AWS account isolation makes it easy to identify and implement security rules and vary developer , dev-ops and operations access based on the account.
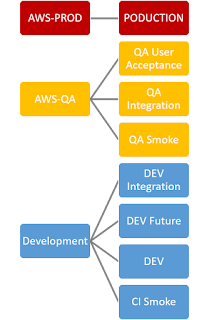
The diagram at right shows a typical 3 account set-up where some of the accounts contain multiple environments. Our company actually has over 20 accounts used for various pre-prod, prod and partner purposes
The AWS Console.
The AWS console lets a user operate in a single account at one time. Enterprise users log into the AWS console with Federated User ids that can provide access to some portion of that Enterprise's accounts. The console displays the AWS Account Alias and some permission and user id information at the top of the screen. It can be tedious to read that information when switching between AWS accounts in a short period of time.
A Chrome Extension
One of the developers on my team wrote a Chrome Plugin that highlights he AWS account information. The plugin provides bassic account information for non-federated accounts like personal or standalone accounts. It optionally color codes a banner at the top of the screen based on some very simple rules related to Account (alias) names. You can find this plugin
- in the Chrome Store under AWS Identity Banner
- on Naveen's GitHub that is the source of the plugin in the Chrome Store
- my forked GitHub
Samples
Standalone Account
Non federated accounts are all treated the same.
Federated Accounts
With QA or QC in the Aws account name in any case or capitalization
Any other Account name string.






Comments
Post a Comment