DNS for Azure Point to Site (P2S) VPN - getting the internal IPs
I wanted to access all my Azure resources without making any of them
visible to the Internet. The easiest give my local machine access to everything on my Azure Virtual
Network (VNET) was to connect to it over VPN. It turns out creating Azure
VPN gateways and connecting to Azure VPN endpoints is easy. There are
some subtleties in getting DNS name resolution to work that can confuse when
first starting out.
Setting the Stage
There are a few ways to get to Azure endpoints and resources that are blocked from the internet. We can
- Create a Point-to-Site connection from our local machines to Azure Network Gateways
- Create a Site-to-Site network connection from our local networks to Azure Network Gateways.
- Use Bastion Hosts
- Use Cloud Shell
- Leave everything open to the internet.
I chose a Point-to-Site (P2S) VPN connection that connects from my laptop
to a VNet Gateway. That joins my laptop to that VNet. Sample
Infrastructure as Code templates and scripts are on GitHub.
Creating a Point-to-Site VPN in Azure
VPN services are tied to VNet Gateways. This means you have to have a VNet to gateway into and a set of subnets. You will have subnets for your workloads and a subnet for the gateway itself. The gateway will present itself using Microsoft Azure public IP addresses.
Your local machine will open a connection to the VPN Gateway Public
IP. The gateway will give the local machine an IP on the VPN tunnel
and create related IP in the gateway subnet.

|
| Click to Enlarge |
Video
DNS over VPN
Azure resources can have some combination of public and private IP
addresses. The public addresses are returned by Azure public
DNS. The private addresses are returned by DNS internal to
Azure. This means that we want to use DNS internal to AZure when
accessing resources over a VPN connection. The VPN tunnel is inside Azure
on our VNet.
The VPN connection will add the IP addresses of any DNS servers that were
configured into the Virtual Network Gateway's DNS server list.
We must add a DNS server to the VNet if we want DNS
support for P2S or S2S connections. You must stand up your own DNS Server,
actually a forwarder, and add it to the VNG DNS server list. Azure
does not provide any DNS server that is addressable from
the VPN connection.
There is no pre-baked recipe for standing up a DNS server in Azure to tie
to the VNG. Most people create a VM with BIND on it. I use an Azure
Container Instance in my environments because I am lazy and provisioning
BIND in a container is a single call to the ACI. I used this project
with zero
modification https://github.com/whiteducksoftware/az-dns-forwarder.
- Create a VNet
- Create necessary Subnets including a subnet for the Gateway
- Create a VNet Gateway
- Create a Point-to-Site VPN server in the VNet Gateway
- Deploy a DNS forwarder. I created a subnet for infrastructure ACI deployments and deployed there.
- Add the DNS forwarder to the VNet
- Download the VPN configuration file and load it into your VPN
- Connect to Azure using client VPN software
- Verify name server lookups return the internal IP addresses.
Troubleshooting DNS
- Verify your VPN is connected.
- Check to see if your nameserver lookups return internal or external IPs.
- Verify there is a DNS server on the VNET the gateway is bound to
- Verify the DNS server is listed in the generic VPN config file you downloaded.
- Verify the DNS server is in %homedir%\AppData\Roaming\Microsoft\Network\Connections\Pbk\rasphone.pbk
- Check to see if the priority of your VPN tunnel is higher than the network connection you connect to the internet with, usually ethernet or wi-fi.
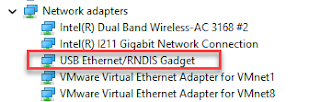
Checking Network Metrics and priorities
The VPN tunnel should have a higher priority (lower index and Metric)
than the NIC connection it rides on top of. This means the PPP
connection should come before your Ethernet or
Wi-Fi connection.
Problem with Network Interface Priority
Azure internal names resolve to external IPs event while on the
VPN. External DNS is used when ethernet is connected because
Ethernet Metric is the same as the VPN tunnel with a lower index than
the VPN connection.
You can see the Index/Metrics for each network interface and can see
the DNS server used and the IP returned.
PS > netsh interface ipv4 show interfaces
Idx Met MTU
State
Name
--- ---------- ---------- ------------
---------------------------
60 25
1400 connected FsiExample-VNET
1 75 4294967295
connected Loopback Pseudo-Interface 1
23 70
1500 disconnected Wi-Fi
4 25
1500 connected Ethernet
5 25
1500 disconnected Local Area Connection* 1
12 65
1500 disconnected Bluetooth Network Connection
25 25
1500 disconnected Local Area Connection* 2
24 15
1500 connected vEthernet (Default
Switch)
11 35
1500 connected VMware Network Adapter
VMnet1
20 35
1500 connected VMware Network Adapter
VMnet8
19 35
1500 connected Azure Sphere
56 15
1500 connected vEthernet (WSL)
PS > nslookup
fsiexample0storage.blob.core.windows.net
Server: Fios_Quantum_Gateway.fios-router.home
Address: 192.168.1.1
Non-authoritative answer:
Name: blob.bn9prdstr05a.store.core.windows.net
Address: 52.239.174.132
Aliases: fsiexample0storage.blob.core.windows.net
fsiexample0storage.privatelink.blob.core.windows.net
Example Fix
Azure internal names resolve to external IPs when ethernet is connected
because Ethernet Metric is the same as the VPN tunnel with a lower index
than the VPN connection.
I unplugged my Ethernet cable which made Wi-Fi be my network
connection. The VPN connection now takes priority over the wi-fi
connection. DNS queries now return the internal IP
You can see the Index/Metrics for each network interface and can see
the DNS server used and the IP returned.
PS C:\Users\joe> netsh interface ipv4 show interfaces
Idx Met MTU
State
Name
--- ---------- ---------- ------------
---------------------------
60 35
1400 connected FsiExample-VNET
1 75 4294967295
connected Loopback Pseudo-Interface 1
23 45
1500 connected Wi-Fi
4 5
1500 disconnected Ethernet
5 25
1500 disconnected Local Area Connection* 1
12 65
1500 disconnected Bluetooth Network Connection
25 25
1500 disconnected Local Area Connection* 2
24 15
1500 connected vEthernet (Default
Switch)
11 35
1500 connected VMware Network Adapter
VMnet1
20 35
1500 connected VMware Network Adapter
VMnet8
19 35
1500 connected Azure Sphere
56 15
1500 connected vEthernet (WSL)
PS C:\Users\joe> nslookup
fsiexample0storage.blob.core.windows.net
Server: UnKnown
Address: 10.0.1.196
Non-authoritative answer:
Name:
fsiexample0storage.privatelink.blob.core.windows.net
Address: 10.0.1.4
Aliases: fsiexample0storage.blob.core.windows.net
Sample GitHub project
https://github.com/freemansoft/vnet-p2s-vpn-bastion-azure


Comments
Post a Comment