Creating Service Accounts for programmatic access to Google Drive APIs
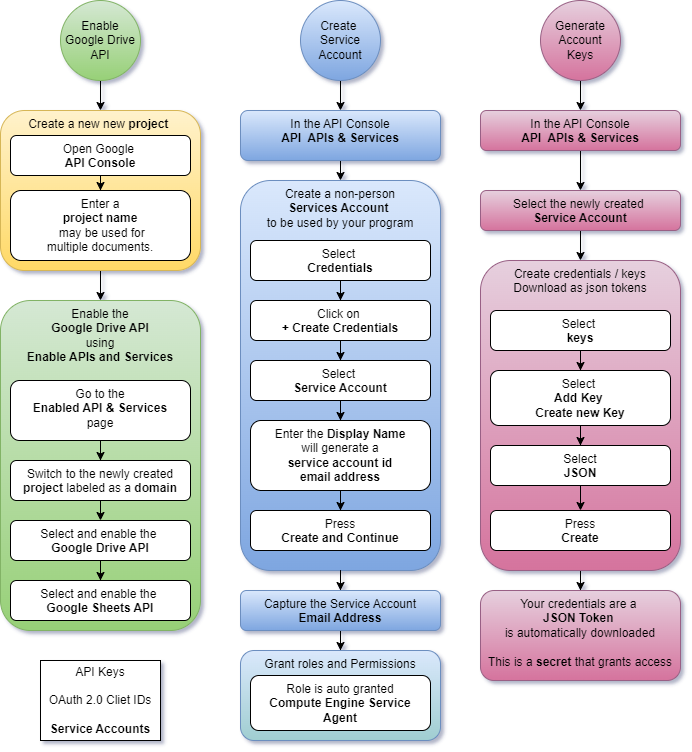
Google Drive is one of those cloud technologies that democratized cloud access to data storage. It lets you securely push all kinds of data into and out of the cloud via Google-provided APIs. APIs and documents are bound to permissions, roles, and identities. Programs accessing Google Docs require credentials, preferably least-privilege credentials, which exist just for a single program's needs. Google IAM supports Service Accounts that are not tied to any human . They can be enabled and disabled without impacting individual users. Accessing Google Docs via API means you have to enable Google Drive API in a project, create an identity/credentials for the program, and then give the identity access to the docs or the API. There are plenty of good tutorials that walk you through setting up an account. They are often light on the overall process or how the steps tie together. It can be confusing the first time or 10 you go through it. Google services are...