It is hard to not leak PII when redacting screen shots with some editor programs
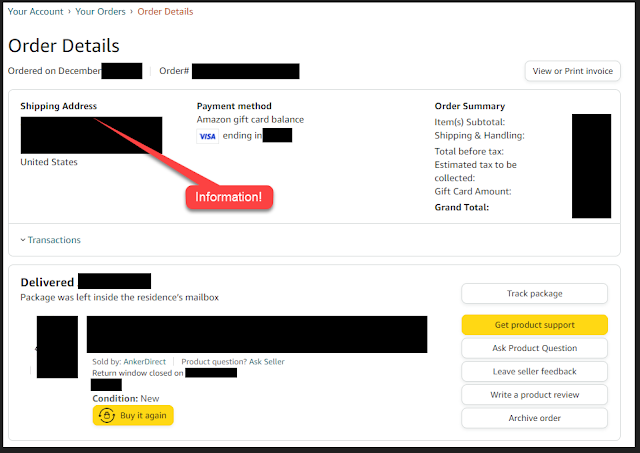
I ran into a situation recently where I almost leaked some private data when using a sanitized screenshot. I took a screenshot of an order screen and then marked out all the PII. The programs retain the original image and editing information inside the image so that you can re-edit it later. This means that anyone else can re-edit unless you protect yourself.
I'm still not sure if I did a transitory upload into some cache before fixing this.
TLDR
Flatten or screenshot any editable PNG files. The latter works for every image.
Creating and Using the Image
This image started off as a Windows 10 snip screen capture. I then redacted the private information with black squares. Later I came back and adjusted the squares to hide data. I copied the image into a Powerpoint presentation and did a talk. There was no risk up to this point.
My solution
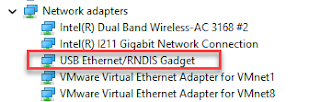
I exported the Powerpoint as PNGi mage files. The image files are flattened images of all the rendered components and are not editable PNG files.
Risky Behavior
- The editable power point is, well, editable. This means someone could edit the PowerPoint, copy the image and then edit the image with the original editor if they could guess which one it was. The editing metadata might still be there.
- Putting the redacted image on the blog has the same risk. Anyone could download the PNG from the blog and have a reasonable chance of editing the image and removing the redactions.
Options
- Export the image without any editability enabled.
- Take a screenshot of the image after editing it.
- Flatten the image using the editing tool.


Comments
Post a Comment